Oracle under attack: 241 critical vulnerabilities your infrastructure can't ignore
The Oracle Database vulnerabilities are back in the news. In April 2026, Oracle released its quarterly critical security update (CPU) with patches for 241 vulnerabilities, 18 of them classified as critical. If your organization uses Oracle Database, MySQL, WebLogic, GoldenGate or any other product in the Oracle ecosystem, you need to take action.
In summary: Oracle has released 241 security patches in April 2026, including 18 critical vulnerabilities affecting Oracle Database Server, MySQL and dozens of additional products. Without an up-to-date asset inventory, it is impossible to know if you are exposed.
What are Oracle Database vulnerabilities and why do they matter?
An Oracle Database vulnerability is a security flaw in Oracle database software that can be exploited by attackers to access, modify or destroy data, escalate privileges or compromise connected systems.
Oracle releases its patches on a quarterly basis through the Critical Patch Update (CPU)a consolidated process that groups together all the failures detected in the previous period. This means that weeks of exposure can accumulate between upgrades if you don't have visibility into which versions are deployed in your organization.
Key points:
- Oracle releases security patches 4 times a year (January, April, July, October).
- The April 2026 CPU includes 241 vulnerabilities in more than 100 Oracle products.
- 18 of these vulnerabilities have critical severity (maximum CVSS score).
- Affected products include Oracle Database Server, MySQL Server, WebLogic, GoldenGate and OCI.
- Without an up-to-date asset inventory, it is not possible to prioritize and execute the correct patches.
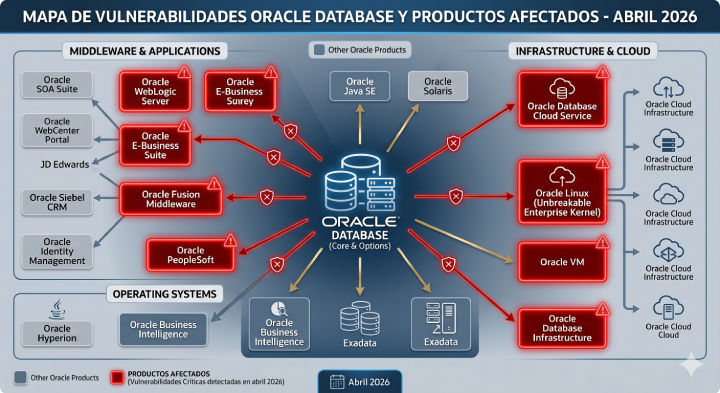
Most critical Oracle products affected in April 2026
The notice published by INCIBE-CERT on April 22, 2026 details the products with the highest risk. These have the greatest impact on typical business infrastructures:
Oracle Database Server (versions 12.1.0.2 to 23.26.1) - the data core of thousands of organizations in Spain and LATAM. 8 new security patches specific to this product.
MySQL Server (versions 8.0 to 9.6) - widely used in web applications and hybrid environments. It also affects MySQL Workbench, MySQL Shell and MySQL Connectors.
Oracle WebLogic Server (versions 12.2.1.4 through 15.1.1.0) - critical in enterprise middleware environments.
Oracle GoldenGate - 10 new patches for the real-time data replication engine.
Oracle REST Data Services and Graph Server - relevant for modern and cloud architectures.
The real problem: you don't know which Oracle versions you have deployed.
Herein lies the real risk. It's not just applying the patch - it's know what needs to be patched.
In medium to large organizations, the Oracle ecosystem may be distributed across multiple servers, development, pre-production and production environments, cloud instances (OCI) and legacy systems. Without an up-to-date and automated software inventory, the vulnerability response process becomes an inefficient and error-prone manual search.
The consequences of not having visibility are:
- Vulnerable versions that remain unpatched for weeks or months.
- Non-compliance with the ENS (National Security Scheme) or NIS2.
- Exposure to failed audits and regulatory sanctions.
- Attack surface unknown to the security team.
How does Proactivanet help manage Oracle Database vulnerabilities?
Proactivanet includes a module for technology asset inventory that automatically detects and registers all Oracle DBMSs deployed in the infrastructure, including installed versions, location (on-premise or cloud), upgrade status and dependencies.
This means that, in the event of an alert such as the April 2026 CPU alert, the IT team can respond within minutes:
- Identify which Oracle instances are affected by each CVE.
- Prioritize patches according to criticality and actual exposure.
- Document the remediation process for regulatory compliance.
- Repeat the process in an agile manner in each quarterly Oracle cycle.
In addition, the new inventory module of Oracle Cloud Infrastructure (OCI) extends this visibility to cloud assets, enabling unified on-premise + cloud management from a single platform.
👉 Discover Proactivanet's asset inventory module.
👉 How Proactivanet helps ENS and NIS2 compliance
Best practices for responding to Oracle CPU
Managing Oracle Database vulnerabilities efficiently requires a repeatable process. These are the key recommendations:
- Sign up for INCIBE-CERT alerts to receive CPU Oracle notifications every quarter.
- Maintain a dynamic inventory of all installed Oracle products, with exact version.
- Prioritize by CVSS criticality - CVEs with a score of 9.0+ are the first to be remediated.
- Test patches in staging environment before applying them in production.
- Document every action for regulatory compliance (ENS, NIS2, ISO 27001).
- Extend visibility to OCI if you have Oracle workloads in the cloud.
🔗 Reference source: INCIBE-CERT Notice - Critical Oracle Updates (April 2026) (external link DoFollow)
Do you know exactly which Oracle versions you have in your infrastructure?
If the answer is not an immediate "yes," there is a visibility gap to resolve before Oracle's next CPU in July 2026.
Proactivanet helps you take full control of your Oracle inventory - on-premise and in OCI - so that no critical vulnerability goes unnoticed.
👉 Request a free demo and discover how thousands of organizations manage their Oracle ecosystem with Proactivanet.
Frequently Asked Questions about Oracle Database Vulnerabilities
- How often does Oracle release security updates? Oracle publishes its Critical Patch Update (CPU) on a quarterly basis, in January, April, July and October. Each release groups together all security flaws detected since the previous cycle. It is essential to have an inventory of the installed versions before each cycle in order to be able to act quickly.
- Do these vulnerabilities also affect Oracle Cloud Infrastructure (OCI)? Yes. The April 2026 CPU includes patches for OCI components such as Management Cloud Engine and other Oracle cloud services. If your organization has migrated workloads to OCI, you need to extend your asset inventory to the cloud environment as well.
- What is the regulatory risk of not patching Oracle vulnerabilities in time? Failure to apply critical patches within a reasonable period of time can result in non-compliance with the National Security Scheme (ENS), the NIS2 directive or ISO 27001, depending on the industry and type of organization. In the event of an incident, the absence of a documented vulnerability management process increases the organization's liability.
IT Service Continuity Management: Preparing your business for the unexpected
